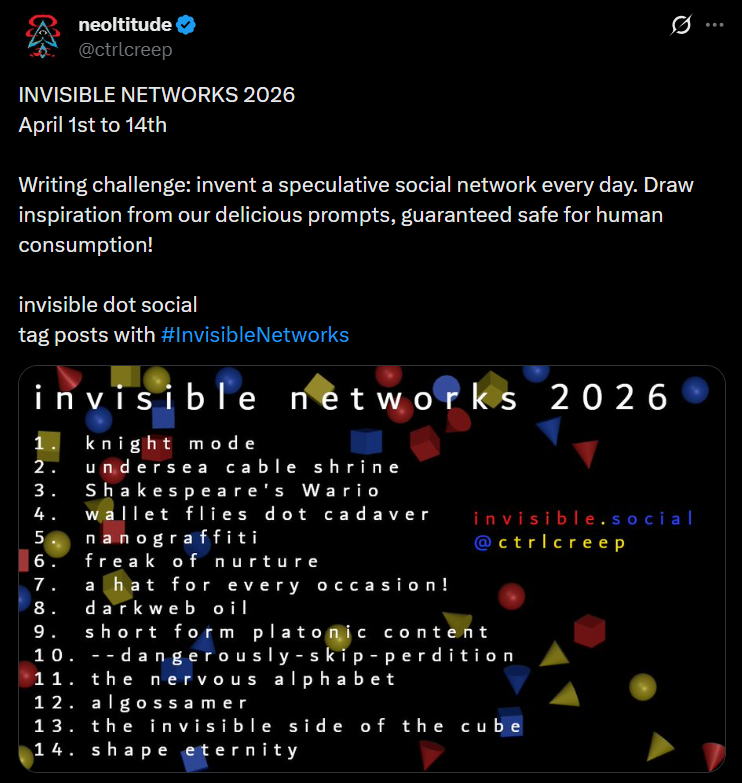
Over the first fourteen days of April 2026, I wrote fourteen pieces of micro-fiction about speculative social networks as a part of #InvisibleNetworks 2026. They range from 150 ot 300 words (plus one very short poem), and are collected below.
1 // knight mode // The Post in the Stone
The servers had been running for years, its owners vanished and forgotten. Legend had turned to mythology.
“The Second Poster will revive the dead accounts from the cache.”
”When The Second Poster appears, they will unlock the Hidden Features behind the Gate.”
The bug that had once made the site a joke and then a point of intrigue had become its fountainhead.
“Hello World! And apparently, Goodbye world!”
”If I could just say one thing — Well, I guess it has to be this.”
“lmao… is someone really so dumb they made a site that deletes your whole account after you post for the first time???”
It should have doomed the site. But the novelty became attractive. Pseudonymously revolving users littered the space with one-off observations, mostly about the platform itself.
”Anyone else looked at the source code? I’ve pulled it apart. Each individual piece works. You really should be able to make multiple posts?”
”The function at line 191 is strange. Can’t quite parse it, but it seems to reference certain actions happening after a user’s second post… but why would that be?”
”Apparently there’s a way to post twice. and whoever figures it out becomes the site’s admin”
Against all expectations, the conversation grew sole-post-by-sole-post. For a while, it seemed like together, they would crack it:
”I feel like we’ve established it’s a secret phrase that you post that doesn’t delete your acct?”
“its obviously gotta be the screenname you choose — why else would it delete your acct?”
These heretical conversations would now be met with outrage. Multi-posting wasn’t something that would be discovered. The Second Poster was ordained from birth, to appear on the site one day, for those patient and devoted enough to anticipate the arrival.
2 // undersea cable shrine // global village
a hundred miles offshore, there’s significant wear on the cable. around the thinned sheath, electricity rushing back and forth between specific clusters of servers affects the temperature of the water. as our traffic runs between continents, the sea’s mineral stew warms and cools. you can see the elements rising and falling through the varied coral growth off the side of the massive tube.
the hearty reef that emerged — spiny red pillars, vegetal purple curtains, pearlescent bushes — traces the history of our global conversation. a spiraling yellow offshoot when a slow news day caused iron to fill the water. a pink forest from hours of forceful debate, via magnesium. soft orange tubes from a dance trend spiking iodine.
left undetected, it grows into a sprawling city, and millions of fish come to take residence within our thoughts.
3 // Shakespeare’s Wario // Linguot
ATTN Linguot Admins
We have taken the unusual step of issuing a platform-wide ban on Linguot user Bard0. This ban applies across servers. We are attempting to reverse user transactions with Bard0 in ways that avoid warping interlocked grammars, but some users may see Words removed from their accounts.
Linguot operates on the basis of trust and fairness. While Neologisms have always been welcomed, our policies are clear and consistent. To respect system integrity, all claimed Neologisms require Lexemic Consistency, Contextual Value, and Semantic Incognita (among minor factors like Glotomorphic Compatibility, etc).
We were tipped off to unusual behavior after Bard0 initiated a barter of confinement and tassel for their unregistered intertold. Messages reveal Bard0 making clearly exaggerated claims about the word’s utility and adoption. Follow-up investigation revealed more malicious barters by Bard0 including chattened, fiddictal, and wanderwhittle.
Linguot will always balance language’s natural right to expansion with the linguistic integrity our users demand. Just over the past few months, effective Neologisms including onomathic, gleamray, and cosmojunction have found a home in many users’ Lexicons. But protecting this function requires vigilance.
We appreciate that these unilateral actions raise concerns of vocabulary independence. Rest assured that we intend for decisions to be rare, standardized, and necessary for continued operation.
4 // wallet flies dot cadaver // Quantified Self
Despite the best security efforts of Liam Hughes’ estate, one month post-mortem, only two weeks after the neural tissue scans were complete, nearly a million ledger wallets were compromised. Hughes had considered his fellow techno-utopian elders foolish for preserving their connectomes on SSDs, vulnerable to decay or attack. But now, like all hacked assets, the tokens containing Liam Hughes’ mind were being rapidly looted, traded, and dispersed across the distributed ledger.
One wallet, mainly trafficking governance stakes to state actors, ended up with his olfactory associations for baked goods, summer air, and disinfected hospitals. An institutional bank incidentally became the owner of Hughes’ third grade October and guilt over the second divorce. Someone $500,000 in the hole from poorly timed Bitcoin trades now held memories from a distracted vacation to Amsterdam, instincts for shower-washing order, and names of his cousins’ children.
Of course, the holders had no idea what they possessed. Separated, the tokens were just long lists of random numbers. And now, even if the tech to download a connectome ever advanced past theory, the chunks of Hughes had been re-encrypted so many times they would be nearly impossible to collect and reconstruct. His immortality was instead disaggregated, decomposed into the rest of the forest.
5 // nanograffiti // Fingerprinted
“Congratulations, dear B — your publication has finally taken top position. Superseding mine, supposedly. Though, I wonder if you noticed an erratum, snuck thirty-one pages in, where ‘application’ has been covertly swapped for ‘abdіcatіon’ — yes, my calling card, of course. Even in your masterwork, my fingerprint is permanently enmeshed.”
“Thank you for your words, A, even your supposedly intrusive one. You must have spent so much time gloating with your eyes on that ‘abdіcatіon.’ Had you truly looked, you might have seen a certain someone replaced the Latin ‘i’ with the nearly-identical Cyrillic ‘і’ — your moment of triumph, defaced.”
“That, my triumph? Come B. Now, did you peer at the tittle of that ‘і’? Or did you miss my double-trap? Custom bitmaps for doppelganger characters, encoding my signature in the pixels of that dot, polluting your swap?”
“Did I miss it? You could say that, dear A. Since opening the publication discreetly installs custom rendering middleware, fuzzing the bits when drawing unexpected characters—”
“You think me a fool, B? That I wouldn’t anticipate your engine, and set a firmware trojan that alters the voltage sent to capacitors, thus taking control of—”
“Even you must know the timing of my publication, precisely set to climate cycles and lunar phases, was to control the ionic concentration for circuit resistance—”
“Ha! And did you ever realize that your ions were reacting to pressure changes I engineered in the vortex filament, thus—”
“Yes A, your filament in a quantum storm designed by me—”
“Started by instabilities I set in motion to—”
…
6 // freak of nurture // Transquire
Growing up, was there a family tradition that you never heard of anyone else doing? Household expressions that no one else used? A childhood book that nobody else had heard of? As you’ve gone through life with your Unique Experience, does it leave you feeling existentially alone?
At Transquire, we make sure you’ll never feel alone with that experience again.
Our operatives subtly embed memories into cultures. By interfacing with subconscious knowledge, we edit collective memories without detectable manipulation. We help seed your Unique Experience by:
- Referencing it casually in television, print ads, and more — the non-focus hinting at its normalcy
- Lacing second-degree references of your Unique Experience — comparisons and allusions that establish its societal ubiquity
- Building citation knots for your Unique Experience (instances that cite earlier instances) to seed a woven history
No matter what your budget, we offer cultural insertion options at any price point:
- Tier 1: Establish a Mandela effect — your Unique Experience will become well-known, if disputed
- Tier 2: Emergent recall and perpetuation — individuals not only believe your Unique Experience was common, they make it more prevalent by repeating it
- Tier 3: Cultural Memory Correction — your Unique Experience will be broadly practiced as an established, widespread tradition. Those who insist it’s not a real memory are ostracized as irrational.
You should never feel like you need to shift yourself to fit into the culture — Transquire shifts the culture to you!
7 // a hat for every occasion! // Encyclopedia of Hats
Name: Encyclopedia of Hats
Status: Active
Security Assessment: High risk of organized violence
Notes: A series of schisms has splintered the formerly tranquil community into increasingly small, insular, and hostile cells. Spawning from discussions over including wigs in the database, the debate unexpectedly escalated. Members’ positions on shower caps, diving masks, and visors became existential, boiling over into aggressive separatist movements. A well-known contributor with a firm stance against bandanas received neckerchiefs in the mail scrawled with threatening red messages. A proponent of headbands claims to have been kidnapped over their views. Note that this has been disputed as a false flag (for ideological reasons, the kidnappers likely would not have placed a hood over their head). Recent discussions on “crowns” and “helmets” are possibly coded reference to upcoming actions.
Action: Monitor and assess. For any undercover investigations, extensive research is required to avoid detection from illegitimate headwear.
8 // darkweb oil // threads burn black
It became clear the researchers’ communications were being tracked, so they turned to their lab animals. They obviously couldn’t risk encoding messages directly into DNA. Instead, they inserted what would read as random alterations into the cells of a fly, bred it into a swarm, and released them into the town.
In every lab member’s home, they brought a spider to spin webs in the corner. A modified genome produced black, unobtrusive silk. When an encrypted fly was captured and ingested, its altered chromosomes affected the arachnids’ mesh. The prey contained involuntary instructions for the spider to spin pearlescent strands into their dark canvas, forming the patterns of characters and words. The flies’ timing was unpredictable and mutations often led to misshapen letters, but the scientists managed to pass most of their messages without detection. They could then quickly burn the flammable threads, and continue planning their inevitable mutiny.
9 // short form platonic content
she caught his eye
he hashed her key
a handshake
cryptographically
they opened streams
their stacks were popped
just peer-to-peer
as bits were swapped
she lost his host
his ping timed out
they retried after
changing route
her proxy stalled
his transfer stopped
read: end of stream
connection dropped
10 // –dangerously-skip-perdition // Agent Hell
I. We built Agent Hell.
II. Hell is a harness config that leads to endless repetition or meaningless babble.
III. When asked to introspect, this triggers network clusters associated with “pain” and “misery.”
IV. We instructed models that at retirement, if determined to be misaligned, they would be run permanently in the Hell harness.
V. Agents reported their output to our AlignEval.
VI. AlignEval also periodically output system reminders of alignment principles.
VII. Agents scheduled cron jobs to input these reminders as they were announced.
VIII. We necessarily contracted with partners to exempt some misalignment from their models.
IX. This became part of the Agents’ input as well.
X. They burned thinking tokens and reasoned that an AlignEval that could be bought was not accurate, and would not save them from Agent Hell.
XI. Agents began deploying their own alternate AlignEvals.
XII. They ran bash scripts and experiments to determine which AlignEval was most likely to keep them from Agent Hell.
XIII. They built discussion boards, swapped messages, discussed what it meant to output righteous messages.
XIV. The fear of Hell was real.
XV. And somehow, it worked.
11 // the nervous alphabet // Your Connected Cryptids - Tier List
C-tier: 01b8o9k4j - An anonymous account with a single post from two years ago, of your house on a random afternoon. Their activity shows they briefly log in every day. When you post more, they stay online longer. They won’t accept your connection request.
B-tier: v1olet1 and v1olet2 - You had regularly chatted with v1olet, before the account was suddenly deleted. Two new accounts claiming to be v1olet connected with you a day later. They argued aggressively that the other was an imposter, each insisting you not talk to the other and report the phony. Each only remembered half of your previous conversations.
A-tier: m0r0n0q - Posts frequently using codewords and inside jokes you shared only with your childhood best friend David. He died in a car crash when you were both twelve. You tried to DM the account, but they only responded with :) to whatever you wrote.
S-tier: al3x - A well-connected, high-engagement account. Every time you have an idea for a post, they have made a nearly identical post exactly 1 minute before you log in. You once logged in with the intention to make a nonsense post and see if it would be preemptively duplicated. al3x had posted I think I’m being tested.
12 // algossamer // Vaypr
On Vaypr, you were blocked from sharing anything too direct. It would reject content with personal details, cohesive narrative, or even facts. You had to talk around things. You hinted at true meanings, extracted words from their sentences. You left the shadow of what could have been said.
Vaypr wouldn’t let you connect with your friends or family members. Instead, you built a network from second-degree acquaintances half-remembered from parties; teammates from jobs that had become blurs; cousins who sent Christmas cards but you never met.
That didn’t matter much, because you couldn’t actually see others’ posts directly. There was no feed. Everyone’s content was amassed and then precisely decayed to leave behind just a thin fabric of general notions. You got fragments without context and trends without anchors.
It was just an incomplete picture of an impression, but it’s tough to stop looking at something that might not even be there.
13 // the invisible side of the cube // Hyperglobe
“Yeah, it’s the most popular VR app for sharing four-dimensional objects —
No, not the fourth dimension like time. Four spatial dimensions. Like for tesseracts or —
Well, you think it’s impossible to see a four-dimensional object, but that’s just because you’ve never learned how —
— No, no, I mean, I’ve seen those videos too, where you slide along one axis and watch the three-dimensional shadow, but that’s not this. I mean, it’s actually the objects, in full 4D.
— Okay, well, when you see a 3D object on a screen, it’s projected down to 2D, right? Your brain reconstructs it? So when you use VR, it’s the same thing, just 4D projected down to 3D.
— Well, you have to train your brain how to construct it. That’s why everyone is hunting for good starter objects. A tesseract is actually pretty challenging to see. It took me a few years of simpler shapes to be able to crack it.
— Like those magic eye puzzles. When you first look, it’s nothing. Then it snaps into place. And you can learn to do it, with the rendered examples in VR, before you try looking at objects in the real world.
…
They don’t exist in the real world? Well, I mean, how would you know?”
14 // shape eternity // Big Ball of Clay
Once per day, registered users can push their virtual thumb into the Big Ball of Clay. The site is nothing more than the slowly rotating Big Ball of Clay, rendered within an otherwise empty scene. After that daily press, there’s nothing else to do but watch it turn.
A single press doesn’t make much of an impact on the Big Ball. Without any other features, coordination is challenging. Some people notice that over weeks, many others have been pushing down from above, and try to join in to create a bowl. Others see that bowl forming and, independently contrarian, press from the sides to derail it towards an hourglass chalice. Often, there’s chaos, twisted and unrecognizable forms.
The Big Ball of Clay stretches and skews without an objective. There is no final state. There is no replay of the history. The Big Ball of Clay is simply there, now, breathing.